Juniper Networks warns Mirai botnet is back and targeting new devices
Share:
Mirai is scanning for poorly protected Session Smart routers. When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works. Operators of the Mirai botnet are back, and looking for easy-to-compromise Session Smart routers to assimilate, experts have warned.
![[Digital image of a lock.]](https://vanilla.futurecdn.net/cyclingnews/media/img/missing-image.svg)
Cybersecurity researchers from Juniper Networks, who recently published a new security advisory, warning its customers of the ongoing threat, noted the malware is scanning for internet-connected Session Smart routers that are using default login credentials.
![[Representational image of data security]](https://vanilla.futurecdn.net/cyclingnews/media/img/missing-image.svg)
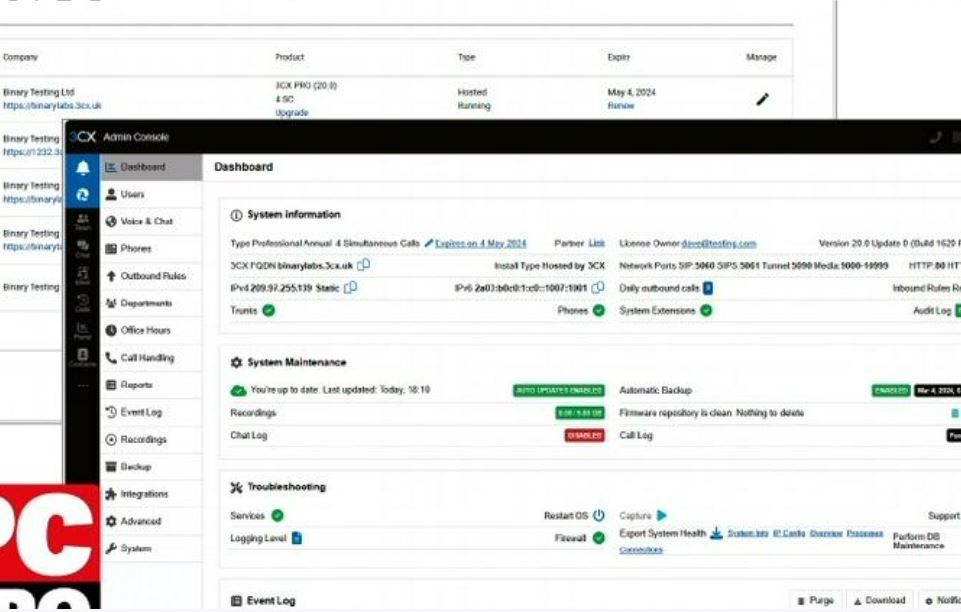
Those that fall into this category are accessed, and used for a wide variety of malicious activities, but mostly Distributed Denial of Service (DDoS) attacks. The campaign apparently started on December 11, and could still be ongoing. "On Wednesday, December 11, 2024, several customers reported suspicious behavior on their Session Smart Network (SSN) platforms," Juniper said in the security advisory. "Any customer not following recommended best practices and still using default passwords can be considered compromised as the default SSR passwords have been added to the virus database.".
![[The TV show posters for The Secret Lives of Animals, The Six Triple Eight and Virgin River season 6 in a collage. ]](https://vanilla.futurecdn.net/cyclingnews/media/img/missing-image.svg)
The best way to protect against the threat is to make sure your internet-connected devices do not use factory login credentials. Instead, they should be protected with strong passwords and, if possible, placed behind a firewall. The Mirai botnet is infamous for targeting Internet of Things (IoT) devices, and then using them to launch massive DDoS attacks. It is also known for exploiting weak or default credentials on devices like routers, cameras, and other IoT hardware. It was first spotted in 2016, but gained notoriety after targeting Krebs on Security in September 2016 and mounting the Dyn DNS attack in October 2016.
![[DDoS attack]](https://vanilla.futurecdn.net/cyclingnews/media/img/missing-image.svg)