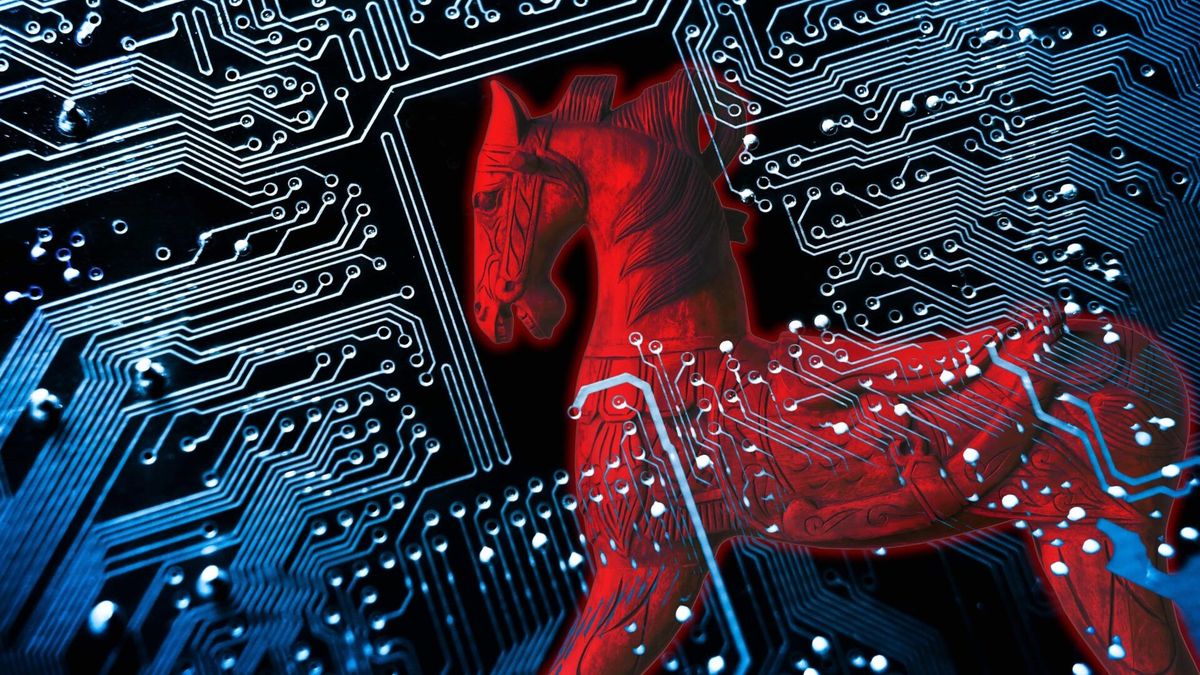
Lumma Stealer campaign silently executes a hidden PowerShell. When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works. CloudSek has uncovered a sophisticated method for distributing the Lumma Stealer malware which poses a serious threat to Windows users.
![[Efosa Udinmwen]](https://vanilla.futurecdn.net/cyclingnews/media/img/missing-image.svg)
This technique relies on deceptive human verification pages that trick users into unwittingly executing harmful commands. While the campaign primarily focuses on spreading the Lumma Stealer malware, its methodology could potentially be adapted to deliver a wide variety of other malicious software.
![[Shopping scams]](https://vanilla.futurecdn.net/cyclingnews/media/img/missing-image.svg)
The campaign employs trusted platforms such as Amazon S3 and various Content Delivery Networks (CDNs) to host phishing sites, utilizing modular malware delivery where the initial executable downloads additional components or modules, thereby complicating detection and analysis efforts.
![[AMD Ryzen 5 7600X processor]](https://vanilla.futurecdn.net/cyclingnews/media/img/missing-image.svg)
The infection chain in this phishing campaign begins with threat actors luring victims to phishing websites that mimic legitimate Google CAPTCHA verification pages. These pages are presented as a necessary identity verification step, tricking users into believing they are completing a standard security check.
![[Quicken Simplifi]](https://vanilla.futurecdn.net/cyclingnews/media/img/missing-image.svg)
The attack takes a more deceptive turn once the user clicks the "Verify" button. Behind the scenes, a hidden JavaScript function activates, copying a base64-encoded PowerShell command onto the user’s clipboard without their knowledge. The phishing page then instructs the user to perform an unusual series of steps, such as opening the Run dialog box (Win+R) and pasting the copied command. These instructions, once followed, cause the PowerShell command to be executed in a hidden window, which is invisible to the user, making detection by the victim almost impossible.